You're Waiting for a Train...

Okay okay, the title of this post has nothing to do with the topic at hand other than the fact that Inception is one of my fave movies. Now that I’ve got that off my chest, let’s talk exploits.
Specifically, what are known as “inception attacks” on VR systems as described in this paper by Zhuolin Yang, Cathy Yuanchen Li, Arman Bhalla, Ben Y. Zhao, and Haitao Zheng of University of Chicago’s Department of Computer Science. Also, Melissa Heillila has a great article on this in the MIT Technology Review.
The Down and Dirty
I’m a man of simple pleasures–SQL injections are more my speed. But this is a seriously cool (it’s really uncool but you know what i mean) attack vector. Note: to my knowledge this attack has not taken place in the wild.
The gist is that an attacker gains control of the user’s interactions with their VR environment, thereby trapping them in an “inception VR layer” that mimics the legitimate VR system. Once trapped in said layer, the user is vulnerable to various means of exploitation.
Of Note
The paper points out two reasons these attacks are/would be so insidious. First, they’re hard to detect, since VR inherently does not resemble more traditional computer applications and therefore makes it difficult for a user to authenticate specific aspects of the experience. Second, and here I’ll quote directly:
an inception attacker can take near total control of the VR experience, not only eavesdropping and recording data, but also altering information and experiences for the target user in real time
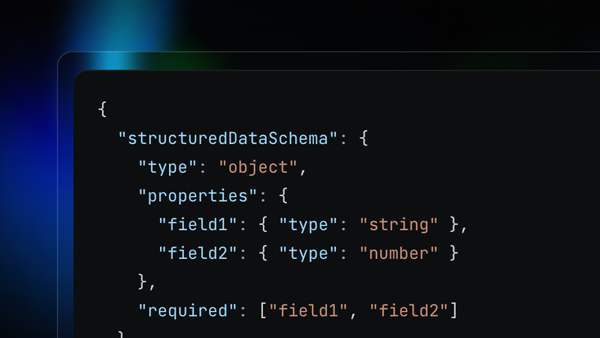
(Below image taken from paper)
My 2 Doge Coins
This is great research, and I highly recommend giving it a quick read. I see this as just another reminder that as tech engagement evolves, so must our personal infosec and awareness. That, and if you haven’t seen Inception, I respectfully demand you do so ASAP.